




Building custom business software requires a delicate balance between user experience and data security. For developers, the most significant hurdle in this process is often the Payment Card Industry Data Security Standard (PCI DSS). Traditionally, handling credit card data meant subjecting your entire infrastructure to rigorous and expensive audits.
The "Zero-Scope" approach changes this dynamic. By shifting the responsibility of handling raw cardholder data away from your servers, you can drastically reduce the compliance burden while accelerating your time to market. This blueprint outlines how to achieve maximum security without sacrificing development velocity.
Zero-scope does not mean ignoring security; it means architecting your application so that sensitive data never touches your environment. When your servers never "see, touch, or store" Primary Account Numbers (PAN), the complexity of your PCI audit drops significantly. This is typically achieved through client-side encryption and hosted fields.
In a traditional integration, a user submits a form, and the data travels to your server before being forwarded to a gateway. This places your server "in scope." In a zero-scope model, the payment form is actually a collection of secure iFrames or hosted fields provided by the payment gateway. The data is sent directly from the user's browser to the secure vault at Integrate Payments.

Developers often debate whether to use a direct API integration or a client-side SDK. For custom business software, the choice impacts both the user interface and the security footprint.
A direct API integration offers maximum control over the checkout experience but requires your server to handle sensitive data, placing you in a high-compliance bracket. Conversely, utilizing a modern JavaScript SDK allows you to embed secure fields directly into your existing UI. This method maintains a seamless look and feel while ensuring the sensitive data is tokenized before it ever reaches your backend.
When choosing your path, prioritize solutions that offer robust recurring billing solutions to ensure that customer data is stored securely for future transactions without increasing your recurring audit requirements.
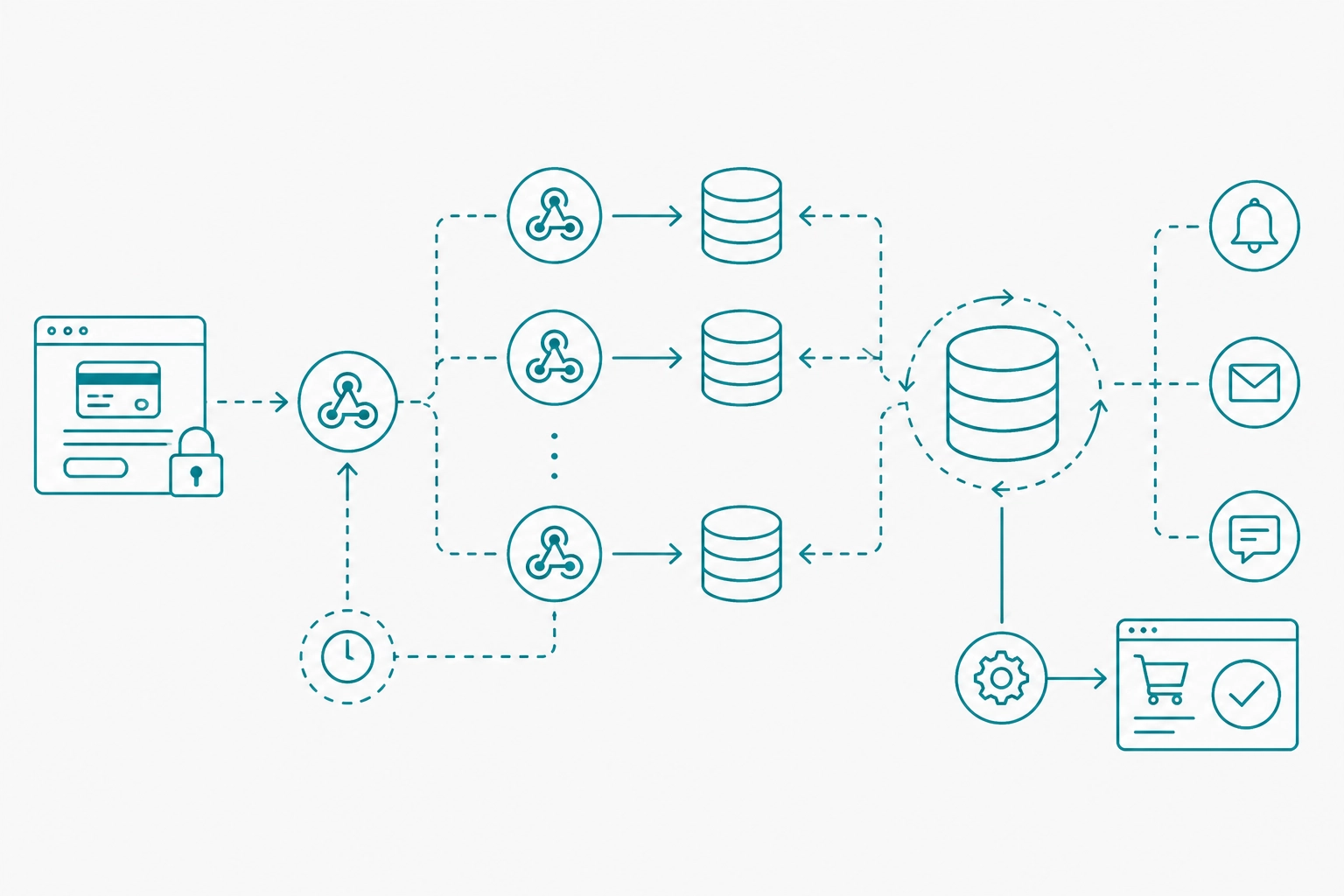
Tokenization is the engine of zero-scope security. When a customer enters their card details into a hosted field, the Integrate Payments gateway replaces that data with a non-sensitive "token." This token acts as a placeholder that your database can safely store and use for processing transactions.
Tokens are mathematically unrelated to the original card number, making them useless to hackers if your database is ever compromised. This architecture is essential for scaling your payment infrastructure as your user base grows. It allows you to build complex features, like one-click checkouts or subscription management, without ever touching raw financial data.
A common frustration for developers is a "flaky" sandbox environment. If the testing environment doesn't mirror production accurately, bugs will inevitably surface during deployment. A stable developer sandbox is non-negotiable for high-quality software development.
Your sandbox should support all transaction types, including voids, refunds, and partial authorizations. It must also provide predictable response codes so you can build robust error-handling logic. Testing against a stable API ensures that when you flip the switch to production, the transition is seamless and your customers experience no downtime.
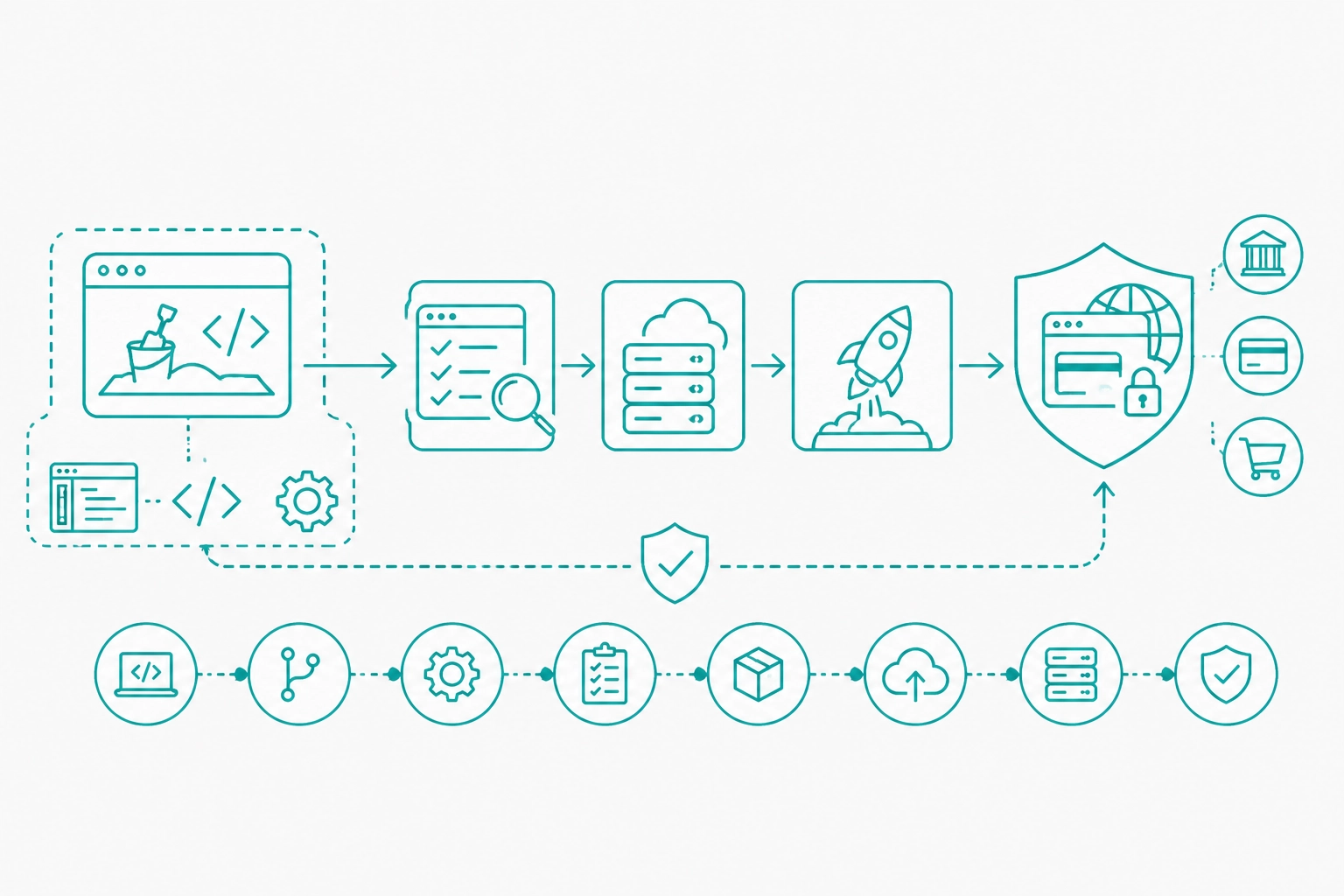
Speed of integration is often the primary KPI for software teams. To move fast, developers need comprehensive documentation, clear code samples, and responsive support. Leveraging pre-built components for common frameworks (like React, Vue, or Angular) can shave weeks off a development cycle.
Integrating with a gateway that supports the Interchange Plus pricing model also provides transparency for the end-user, making the software more attractive to business owners. When the technical integration is straightforward and the pricing is fair, the overall value proposition of your custom software increases.
Many custom business applications, such as ERPs or specialized POS systems, require both digital and physical payment capabilities. Integrating hardware into a software stack can be notoriously difficult due to driver issues and legacy protocols.
To maintain a zero-scope environment in a physical setting, developers should look for cloud-based terminal integrations. By using a payment terminal integration guide, you can connect semi-integrated hardware that communicates directly with the gateway. This ensures that even when a card is dipped or tapped in person, the data stays off the local network and the software remains out of PCI scope.
In a zero-scope architecture, your server is notified of successful payments via webhooks. Managing these asynchronous events is critical for maintaining data integrity. If a webhook is missed, your application might not update an order status or provision a service, leading to customer dissatisfaction.
Implement an idempotent webhook listener to handle duplicate notifications. Your system should log every event and provide a mechanism to "replay" missed webhooks if necessary. This level of engineering ensures that your custom software remains reliable even during high-traffic events or network hiccups.
While zero-scope focuses on the transaction data, overall security involves protecting the entire user journey. Implementing Multi-Factor Authentication (MFA) for your administrative portals and utilizing PCI compliance secure credit card storage are standard best practices.
Furthermore, developers should regularly audit their integration to ensure that no new features inadvertently bring the server back into scope. For example, adding a feature that logs full API requests for debugging could accidentally capture sensitive data if not properly filtered.
As we move further into 2026, the demand for embedded finance continues to rise. Business owners no longer want to jump between different platforms to manage their operations and their money. They want integrated solutions that work out of the box.
By following the Zero-Scope Blueprint, you position your software as a leader in the market. You offer the highest level of security, the fastest integration times, and the most stable user experience. Whether you are building a restaurant management software or a complex B2B marketplace, the principles of data isolation and tokenization remain the gold standard.
Building secure payment flows doesn't have to be a bottleneck for your development team. By abstracting the complexity of PCI compliance through smart architectural choices, you can focus on what really matters: building great features for your users.
For more technical information on implementing these strategies, explore our merchant software integration tools or contact our engineering support team. We provide the documentation and sandbox access needed to get your project from concept to production.



